21st Century Wire says…
This is how public opinion can be softened to accept Central Government control and access to ISP’s and increased censorship laws – via celebrity.
It’s shocking to witness how quickly and eager the establishment media are to seize onto celebrity and high-profile ‘hacking’ stories under the banner of ‘privacy concerns’ – and how predictably, pundits and politicians fuse these events with renewed calls for more restrictions on internet freedom – to “protect celebrities and high-profile individuals” like Hugh Grant, who provided a celebrity brand for the Hacked-Off/Levison Inquiry for state press censorship in the UK. The US are currently lining up a similar celebrity panel of hacking victims.

Celebrities like Grant are used by Government to sell unpopular state repression.
It’s still not clear how the constant focus on highly paid celebrities benefits the public’s own fragile ‘privacy concerns’. Now, let’s take a sober look at this phenomenon…
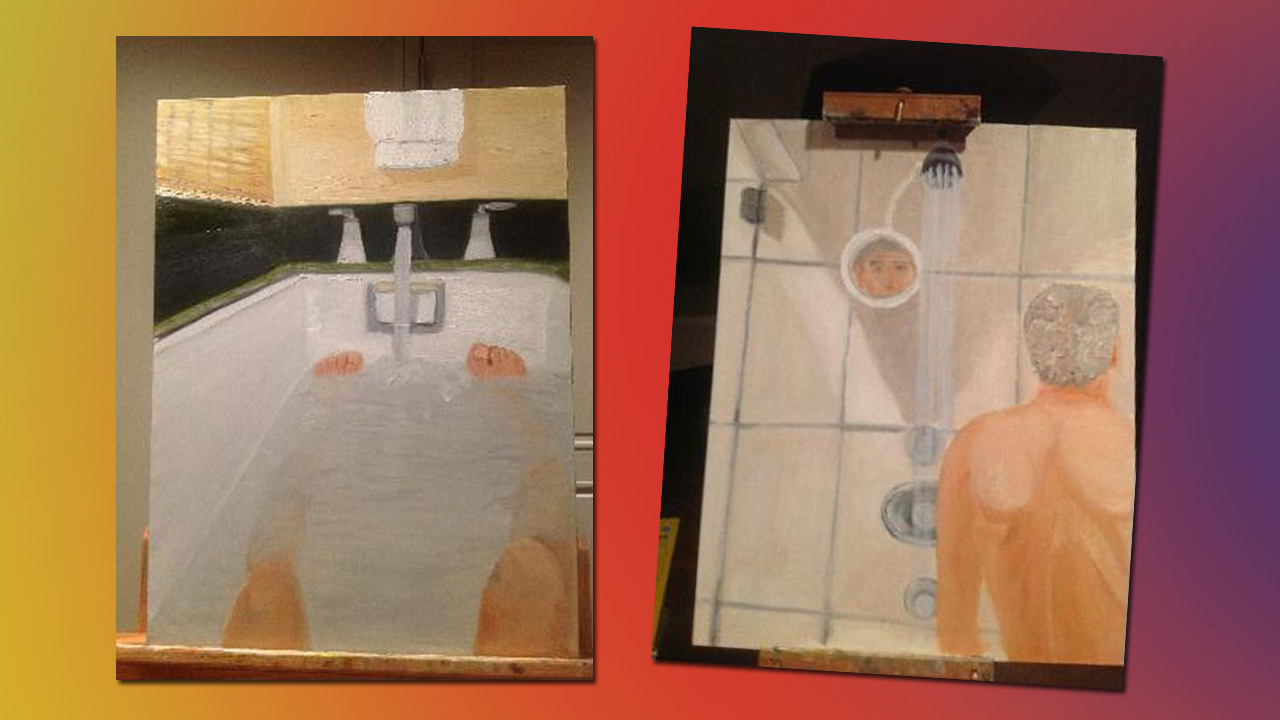
Top among the items leaked online this week, was the discovery of George W. Bush’s hidden talents – a collection of rather camp, David Hockney-like self portraits of himself in the shower (see below) and bath tub. The leak should be a boon and not a victim story for Bush the Younger. Art mogul Charles Saachi could probably make himself and Dubya millions brokering this new Bush/Hockney collection. But we digress…
This latest ‘Bush hack’ in America has been predictably attached with Britain’s notorious phone hacking scandal, even though the two events have no relation whatsoever. None. Not even in a theoretic sense. But watch carefully, how all mainstream media outlets subtly streamline these seemingly unrelated events in order to later declare ‘a crisis’ and aid the state in ramming through emergency legislation which normally erodes rights and liberty. Watch how they do it, recognise the craft, and you will have cracked a very subtle code which runs between central government and the corporate media.
 What should be pointed out here (but wasn’t, of course) by the Washington Post, is that the alleged hacking victim, George W. Bush, himself the enabler of Patriot Acts I and II – the very legislation which gave the US government carte blanc to hack into any American’s email, hack their phone and track them via GPRS – without any warrant, with all data collected kept in a secret file somewhere unknown. Many secret mass surveillance programs were since launched, like Operation Stellar Wind. The same could be argued should Tony Blair’s emails be hacked only to discover a cache similarly camp, sexually compromising photos or love letters, as they happened to turn up in the public domain, theoretically. Like Bush’s police state legislation, it was Blair’s emergency repressive legislation in Great Britain which ultimately gave the UK government agencies Patriot Act powers with total impunity.
What should be pointed out here (but wasn’t, of course) by the Washington Post, is that the alleged hacking victim, George W. Bush, himself the enabler of Patriot Acts I and II – the very legislation which gave the US government carte blanc to hack into any American’s email, hack their phone and track them via GPRS – without any warrant, with all data collected kept in a secret file somewhere unknown. Many secret mass surveillance programs were since launched, like Operation Stellar Wind. The same could be argued should Tony Blair’s emails be hacked only to discover a cache similarly camp, sexually compromising photos or love letters, as they happened to turn up in the public domain, theoretically. Like Bush’s police state legislation, it was Blair’s emergency repressive legislation in Great Britain which ultimately gave the UK government agencies Patriot Act powers with total impunity.
So these political leaders are the one’s responsible for state repression of people’s liberties, and we are meant to think that their being hacked should lead to even more repression. Funny that.
Would the media and government call for internet clampdowns if the hacks exposed Bush and Blair’s involvement in lying, crimes or fraud regarding the Iraq War, 9/11, or the murder of David Kelly?
The day the Washington Post, BBC, CNN, MSNBC, FOX, or any other major media outlet, can point out these obvious ironies in their high-budget reporting, is the day that we may actually be able to reclaim our basic liberties.
Where is this all heading? Through its new laws and restrictions, the American and European governments desire a total monopoly on hacking and spying – and of course, this means eventually, a complete monopoly on all media and communications…
.
‘Bush, Celebrity Hacks Raise Profile of Privacy Concerns’
Hayley Tsukayama
Washington Post
Photos and correspondence from half a dozen e-mail accounts linked to the Bush family, including information about former U.S. presidents George W. Bush and George H.W. Bush, brings discussion of personal online privacy issues into sharp focus.
Members of the Bush family and their close acquaintances found late Thursday that a hacker — self-styled “Guccifer” — bragged about compromising half a dozen Bush family and acquaintances accounts and posted the information online. In an interview with the Smoking Gun, which published the photos and conversation experts, the hacker said that at least some of the photos came from an AOL account belonging to George H.W. Bush’s daughter, Dorothy Bush Koch. A family spokesman confirmed the attack to The Washington Post on Friday.
AOL did not immediately respond to a request for comment on the breach.
The highly personal information in the files, including details about the elder Bush’s hospitalization and painted self-portraits of George W. Bush in the shower [above] — may make many reexamine the kind of information they’re putting online and storing in their e-mail accounts.
And e-mail is not the only avenue for technological privacy invasions. News of the Bush family breach comes as British courts announced that 144 people — including celebrities such as Hugh Grant and Sarah Ferguson, Duchess of York, — would receive damages as a result of the phone-hacking scandal that ultimately ended the run of the British tabloid, News of the World. As the Guardian reported, 17 individuals demanded public apologies from the defunct newspaper’s publisher, News International.
Most people won’t be targets of cyber crime in the same way that high-profile celebrities are, but everyone’s lingering digital footprints provide rich caches of personal information to those who want it.
Cyber criminals are happiest when information is easy to get, so while consumers may not have much agency when it comes to protecting themselves against company-wide attacks, they can make it more difficult for hackers looking to smash and grab attacks on personal accounts.
Using password protection on phones and voicemail is a good first step, as is taking the admittedly painful step of not reusing your e-mail password for other accounts. That reduces the risk that your e-mail will be hacked if you are hit with an attack on an unrelated site. It’s also a good practice for users to take their most sensitive information out of the cloud and store them locally — or on a protected thumb drive if they need the portability. There could be traces of data you delete from e-mail servers that can be accessed by hackers, but there’s certainly no need to make it easy for them.
Related stories:
Microsoft hits Google with e-mail privacy campaign
READ MORE HOLLYWOOD NEWS AT: 21st Century Wire Hollywood Files
–