21st Century Wire says…
The naysayers and loyal liberal guard claim that Obamacare’s RFID or Class III medical device is not in the bill and rumours online are some sort of a hoax. They will also tell you that these brilliant ‘care management’ technologies cannot be used against the people wearing them.
 Note: Page 1004 of the new law (dictating the timing of this chip), reads, and I quote: “Not later than 36 months after the date of the enactment”
Note: Page 1004 of the new law (dictating the timing of this chip), reads, and I quote: “Not later than 36 months after the date of the enactment”
H.R. 3200 section 2521, Pg. 1001, paragraph 1.
“The Secretary shall establish a national medical device registry (in this subsection referred to as the ‘registry’) to facilitate analysis of post-market safety and outcomes data on each device that— ‘‘is or has been used in or on a patient; ‘‘and is— ‘‘a class III device; or ‘‘a class II device that is implantable, life-supporting, or life-sustaining.”
Class III devises are items such as breast implants, pacemakers, heart valves, etc. A Class II device that is implantable is, as you see from the FDA, an implantable radio frequency transponder, RFID chip. From breast implants, to pacemakers, to RFID chips which one is the only possible one that can used for the stated purpose in section B which is, “for linking such data with the information included in the registry”.
RFID chip conduct and in some case, emit heat and electronic signals. The technology’s long-term effects on humans is not yet known, because no long-term, peer reviewed studies have been conducted on them.
Now here’s the real danger…
It couldn’t happen, but suppose it did?
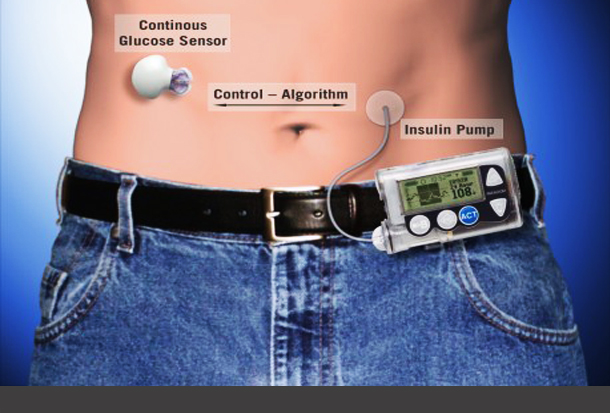
It’s straight out of an episode of Homeland; terrorists hack an implanted medical device and use it to administer a lethal shock to the patient carrying it inside them. As it turns out, hacking implants like pacemakers and insulin pumps is definitely possible, and device manufacturers have known about it for years. It’s taken a small cadre of computer hackers to show the public what companies like Medtronic dismissed as very remote possibilities – large scale device tampering leading to thousands of injuries and deaths. Are they playing a dangerous game of chicken by dragging their feet all this time?
Medical devices are like ‘open doors’
As several professional hackers, including the late Barnaby Jack, pointed out, medical device manufacturers didn’t pay much attention to digital security when constructing their implantable components. Adding additional security features would weigh the devices down, shorten battery life, and make them bulkier. For an insulin pump that’s only about the size of a pager, adding additional weight can make a lot of difference in terms of how much the device costs. Shelling out extra cash won’t make those items popular with insurance companies, and they basically control what devices their policyholders have access to because they make the coverage decisions. In choosing to forego added security options, Medtronic and other manufacturers left their products dangerously vulnerable to ‘interrogation’; a technical term for transmitting a signal to an electronic device to interact with it. Without any encryption, an insulin pump doesn’t even involve the hacker equivalent of opening a door. All they need to do is stroll on in.
The second part of the problem is the increasing dependence on wireless communication for these medical devices to manage patient vital signs and know when to dispense medications. Ever jump onto an open Wi-Fi signal at a coffee shop? No password required. Just log in and surf the web. That’s basically the same principle when a hacker gains control of a device that’s using an unprotected wireless network. Modern pacemakers and insulin pumps – among other implantables – are no different than PCs or Macs when it comes to vulnerabilities. According to Jack, who was working for MacAfee at the time, the lack of security in implanted devices is “really quite shocking.”
Ignoring the problem won’t help
Medtronic, maker of the most widely used insulin pump in the United States, had previously refused to look into calls from Jay Radcliffe, a computer security expert and insulin pump wearer, that their devices were vulnerable to attack. Radcliffe reportedly exposed a security hole in Medtronic’s insulin pump after tinkering with his own device. All it took to interrogate a pump and order it to dump all its chemical contents was a radio transmitter about the size of a human index finger and a laptop computer. He presented the findings at the 2011 Black Hat security conference in Las Vegas, which unleashed a tidal wave of hysterics from parents worried that Radcliffe had essentially given criminals the ability to kill their diabetic children.
Medtronic’s Revel insulin pump retails for $6,000 to $7,000 before insurance coverage kicks in. Imagine spending that much on a product that a hack can take over with a finger-sized radio transmitter. Photo Credit: Flickr
Radcliffe’s findings, despite their media coverage, are not the first to reach the surface. Warnings about possible hacks into Medtronic’s devices – namely their pacemakers and defibrillators – came as early as 2008 when The New York Times published an article detailing the findings of research teams that exploited the samesecurity vulnerabilities Radcliffe would use three years later. Medtronic and others knew the day was coming when they wouldn’t be able to dismiss the concerns of security experts as “remote possibilities” or “low risk.” Did they do enough to close the gaping holes in wireless communication? That conversation didn’t begin in earnest until Radcliffe and Barnaby Jack upped the ante. Jack, famous for making ATMs spit cash with a keystroke at Black Hat, created simple transmitter that could scan a 300-foot wide area for common insulin pumps, interrogate those devices, and force them to dump their contents into the bodies of their wearers. The prospect of high casualties without the need to see targets or come in contact with them in any way must’ve been the fire medical device companies needed. How did computer hackers become one of the most prominent groups advocating for public safety?
Hacker to the rescue?
The public image of a computer ‘hacker’ is one who uses their digital powers for evil stealing credit card numbers and identities, brings down websites and infects computers with nasty viruses and malware. While that’s true for some, there are many “hackers” who wear the white hat; experts who seek to uncover security issues to warn companies before the wrong people discover them. Jack and Radcliffe have acknowledged that their work can be a double-edged sword for the community. In uncovering exploitable holes in security, and informing the public about them, there is the risk that the bad guys will try to use them to do, well… bad things…
READ MORE RFID NEWS AT: 21st Century Wire RFID Files